Sec. Tools. Org Top Network Security Tools. Sec. Tools. Org Top 1. Network Security Tools. For more than a decade, the Nmap. Project has been cataloguing the network security communitys. In 2. 01. 1 this site became much more dynamic, offering. This site allows open source and commercial tools on any platform. Nmap Security Scanner, Ncat network connector, and Nping packet manipulator. Were very impressed by the collective smarts of the security community and we highly recommend reading the whole list and investigating any tools you are unfamiliar with. Here is a list of security tools that have been collected from the internet. These tools are specifically aimed toward security professionals and enthusiasts. No more missed important software updates UpdateStar 11 lets you stay up to date and secure with the software on your computer. Penetration testing The complete guide with top 37 Penetration Testing Tools every Penetration tester should know. Tools review with download link. Uakti Discografia. Acunetix 7 CrackleClick any tool name for more details on that particular application, including the chance to read and write reviews. Many site elements are explained by tool tips if you hover your mouse over them. Enjoy Tools 12. Metasploit took the security world by storm when it was released in 2. It is an advanced open source platform for developing, testing, and using exploit code. The extensible model through which payloads, encoders, no op generators, and exploits can be integrated has made it possible to use the Metasploit Framework as an outlet for cutting edge exploitation research. Ib1xCZHFUVk/UJYYbxBt3OI/AAAAAAAAAFk/0iSHpMNxCuk/s1600/Untitled.png' alt='Acunetix 7 Crack' title='Acunetix 7 Crack' />It ships with hundreds of exploits, as you can see in their list of modules. This makes writing your own exploits easier, and it certainly beats scouring the darkest corners of the Internet for illicit shellcode of dubious quality. One free extra is Metasploitable, an intentionally insecure Linux virtual machine you can use for testing Metasploit and other exploitation tools without hitting live servers. Metasploit was completely free, but the project was acquired by Rapid. The Framework itself is still free and open source, but they now also offer a free but limited Community edition, a more advanced Express edition 5,0. Pro edition. Other paid exploitation tools to consider are Core Impact more expensive and Canvas less. The Metasploit Framework now includes an official Java based GUI and also Raphael Mudges excellent Armitage. The Community, Express, and Pro editions have web based GUIs. Read 1. 6 reviews. Latest release version 4. Dec. 1. 8, 2. 01. Acunetix 7 Crack Full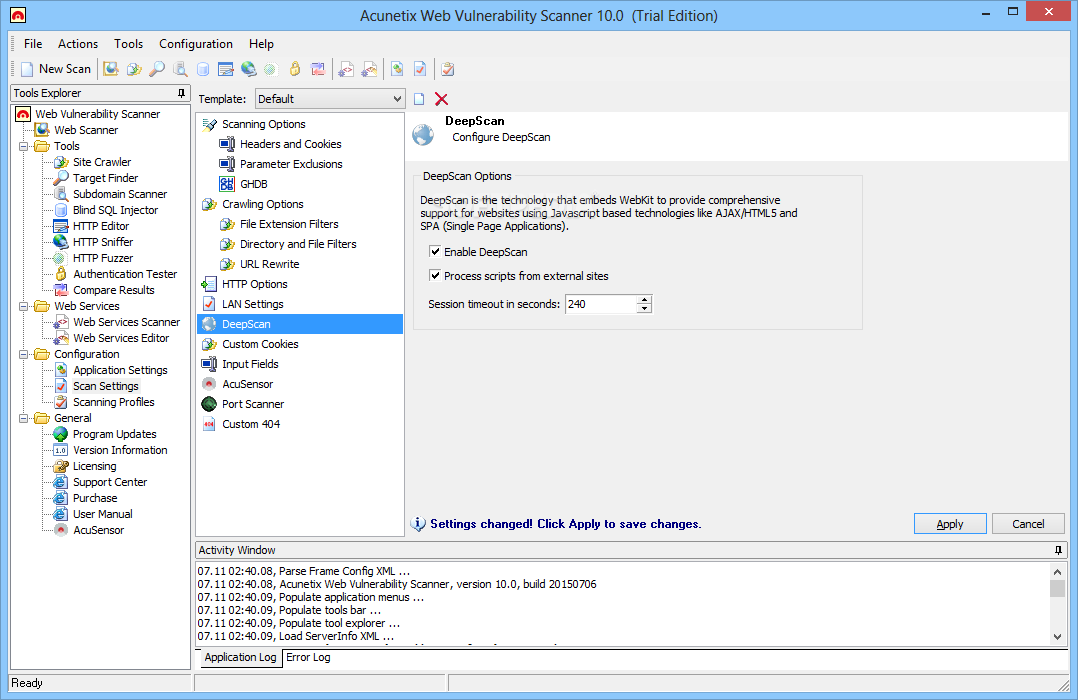 Nessus is one of the most popular and capable vulnerability scanners, particularly for UNIX systems. It was initially free and open source, but they closed the source code in 2. Registered Feed version in 2. It now costs 2,1. A free Nessus Home version is also available, though it is limited and only licensed for home network use. Nessus is constantly updated, with more than 7. Key features include remote and local authenticated security checks, a clientserver architecture with a web based interface, and an embedded scripting language for writing your own plugins or understanding the existing ones. P9zU8WZm84/TP3Gb26S6SI/AAAAAAAAAOQ/fZYaLAyLCvs/s1600/07-Dec-10+12-27-09+malam.png' alt='Acunetix 7 Crack' title='Acunetix 7 Crack' />Read 1. Latest release version 6. Network Footprinting Reconnaissance The tester would attempt to gather as much information as possible about the selected network. Reconnaissance can take two forms. Acunetix CEO Nicholas Galea said Due to recent attacks such as the Sony hack and the Anthem Inc breach, companies are under increasing pressure to ensure their. Ciscos popular VPN Client for 64Bit Windows operating systems. VPN Client version 5. Useful Cisco VPN related articles W. I. Table of Contents. About Armitage Before we begin. Getting Started How to get any woman to talk to you User Interface Tour So many pretty screenshots. March 1. 6, 2. 01. This network intrusion detection and prevention system excels at traffic analysis and packet logging on IP networks. You Need To Install Identd To Use This Server Allows. Through protocol analysis, content searching, and various pre processors, Snort detects thousands of worms, vulnerability exploit attempts, port scans, and other suspicious behavior. Snort uses a flexible rule based language to describe traffic that it should collect or pass, and a modular detection engine. Also check out the free Basic Analysis and Security Engine BASE, a web interface for analyzing Snort alerts. While Snort itself is free and open source, parent company Source. Fire offers their VRT certified rules for 4. Sourcefire also offers a free 3. Read 3 reviews. Latest release version 2. July 2. 3, 2. 01. John the Ripper is a fast password cracker for UNIXLinux and Mac OS X. Its primary purpose is to detect weak Unix passwords, though it supports hashes for many other platforms as well. There is an official free version, a community enhanced version with many contributed patches but not as much quality assurance, and an inexpensive pro version. You will probably want to start with some wordlists, which you can find here, here, or here. Read 1. 1 reviews. Latest release version 1. May 3. 0, 2. 01. 3 4 years, 6 months ago. Burp Suite is an integrated platform for attacking web applications. It contains a variety of tools with numerous interfaces between them designed to facilitate and speed up the process of attacking an application. All of the tools share the same framework for handling and displaying HTTP messages, persistence, authentication, proxies, logging, alerting and extensibility. There is a limited free version and also Burp Suite Professional 2. Read 2. 0 reviews. Latest release version 1. June 3, 2. 01. 1 6 years, 6 months ago. Core Impact isnt cheap be prepared to spend at least 3. It sports a large, regularly updated database of professional exploits, and can do neat tricks like exploiting one machine and then establishing an encrypted tunnel through that machine to reach and exploit other boxes. Other good options include Metasploit and Canvas. Read 9 reviews. Latest release version 1. Aug. 8, 2. 01. 1 6 years, 4 months ago. Disassembly is a big part of security research. It will help you dissect that Microsoft patch to discover the silently fixed bugs they dont tell you about, or more closely examine a server binary to determine why your exploit isnt working. Many debuggers are available, but IDA Pro has become the de facto standard for the analysis of hostile code and vulnerability research. This interactive, programmable, extensible, multi processor disassembler has a graphical interface on Windows and console interfaces on Linux and Mac OS X. Review this tool. Latest release version 6. April 1. 3, 2. 01. Maltego is a forensics and data mining application. It is capable of querying various public data sources and graphically depicting the relationships between entities such as people, companies, web sites, and documents. Maltego is an open source intelligence too, but isnt open source software. Read 1 review. Latest release version 3. Jan. 1. 7, 2. 01. Rapid. 7 Nexpose is a vulnerability scanner which aims to support the entire vulnerability management lifecycle, including discovery, detection, verification, risk classification, impact analysis, reporting and mitigation. It integrates with Rapid. Metasploit for vulnerability exploitation. It is sold as standalone software, an appliance, virtual machine, or as a managed service or private cloud deployment. User interaction is through a web browser. There is a free but limited community edition as well as commercial versions which start at 2,0. Read 1. 2 reviews. GFI Lan. Guard is a network security and vulnerability scanner designed to help with patch management, network and software audits, and vulnerability assessments. The price is based on the number of IP addresses you wish to scan. A free trial version up to 5 IP addresses is available. Read 6 reviews. Latest release version 2. May 1. 9, 2. 00. 1 1. Acunetix is a web vulnerability scanner that automatically checks web applications for vulnerabilities such as SQL Injections, cross site scripting, arbitrary file creationdeletion, and weak password strength on authentication pages. It boasts a comfortable GUI, an ability to create professional security audit and compliance reports, and tools for advanced manual webapp testing. Read 7 reviews. Latest release version 1. Nov. 1. 6, 2. 01. Qualys. Guard is a popular Saa. S software as a service vulnerability management offering.
Nessus is one of the most popular and capable vulnerability scanners, particularly for UNIX systems. It was initially free and open source, but they closed the source code in 2. Registered Feed version in 2. It now costs 2,1. A free Nessus Home version is also available, though it is limited and only licensed for home network use. Nessus is constantly updated, with more than 7. Key features include remote and local authenticated security checks, a clientserver architecture with a web based interface, and an embedded scripting language for writing your own plugins or understanding the existing ones. P9zU8WZm84/TP3Gb26S6SI/AAAAAAAAAOQ/fZYaLAyLCvs/s1600/07-Dec-10+12-27-09+malam.png' alt='Acunetix 7 Crack' title='Acunetix 7 Crack' />Read 1. Latest release version 6. Network Footprinting Reconnaissance The tester would attempt to gather as much information as possible about the selected network. Reconnaissance can take two forms. Acunetix CEO Nicholas Galea said Due to recent attacks such as the Sony hack and the Anthem Inc breach, companies are under increasing pressure to ensure their. Ciscos popular VPN Client for 64Bit Windows operating systems. VPN Client version 5. Useful Cisco VPN related articles W. I. Table of Contents. About Armitage Before we begin. Getting Started How to get any woman to talk to you User Interface Tour So many pretty screenshots. March 1. 6, 2. 01. This network intrusion detection and prevention system excels at traffic analysis and packet logging on IP networks. You Need To Install Identd To Use This Server Allows. Through protocol analysis, content searching, and various pre processors, Snort detects thousands of worms, vulnerability exploit attempts, port scans, and other suspicious behavior. Snort uses a flexible rule based language to describe traffic that it should collect or pass, and a modular detection engine. Also check out the free Basic Analysis and Security Engine BASE, a web interface for analyzing Snort alerts. While Snort itself is free and open source, parent company Source. Fire offers their VRT certified rules for 4. Sourcefire also offers a free 3. Read 3 reviews. Latest release version 2. July 2. 3, 2. 01. John the Ripper is a fast password cracker for UNIXLinux and Mac OS X. Its primary purpose is to detect weak Unix passwords, though it supports hashes for many other platforms as well. There is an official free version, a community enhanced version with many contributed patches but not as much quality assurance, and an inexpensive pro version. You will probably want to start with some wordlists, which you can find here, here, or here. Read 1. 1 reviews. Latest release version 1. May 3. 0, 2. 01. 3 4 years, 6 months ago. Burp Suite is an integrated platform for attacking web applications. It contains a variety of tools with numerous interfaces between them designed to facilitate and speed up the process of attacking an application. All of the tools share the same framework for handling and displaying HTTP messages, persistence, authentication, proxies, logging, alerting and extensibility. There is a limited free version and also Burp Suite Professional 2. Read 2. 0 reviews. Latest release version 1. June 3, 2. 01. 1 6 years, 6 months ago. Core Impact isnt cheap be prepared to spend at least 3. It sports a large, regularly updated database of professional exploits, and can do neat tricks like exploiting one machine and then establishing an encrypted tunnel through that machine to reach and exploit other boxes. Other good options include Metasploit and Canvas. Read 9 reviews. Latest release version 1. Aug. 8, 2. 01. 1 6 years, 4 months ago. Disassembly is a big part of security research. It will help you dissect that Microsoft patch to discover the silently fixed bugs they dont tell you about, or more closely examine a server binary to determine why your exploit isnt working. Many debuggers are available, but IDA Pro has become the de facto standard for the analysis of hostile code and vulnerability research. This interactive, programmable, extensible, multi processor disassembler has a graphical interface on Windows and console interfaces on Linux and Mac OS X. Review this tool. Latest release version 6. April 1. 3, 2. 01. Maltego is a forensics and data mining application. It is capable of querying various public data sources and graphically depicting the relationships between entities such as people, companies, web sites, and documents. Maltego is an open source intelligence too, but isnt open source software. Read 1 review. Latest release version 3. Jan. 1. 7, 2. 01. Rapid. 7 Nexpose is a vulnerability scanner which aims to support the entire vulnerability management lifecycle, including discovery, detection, verification, risk classification, impact analysis, reporting and mitigation. It integrates with Rapid. Metasploit for vulnerability exploitation. It is sold as standalone software, an appliance, virtual machine, or as a managed service or private cloud deployment. User interaction is through a web browser. There is a free but limited community edition as well as commercial versions which start at 2,0. Read 1. 2 reviews. GFI Lan. Guard is a network security and vulnerability scanner designed to help with patch management, network and software audits, and vulnerability assessments. The price is based on the number of IP addresses you wish to scan. A free trial version up to 5 IP addresses is available. Read 6 reviews. Latest release version 2. May 1. 9, 2. 00. 1 1. Acunetix is a web vulnerability scanner that automatically checks web applications for vulnerabilities such as SQL Injections, cross site scripting, arbitrary file creationdeletion, and weak password strength on authentication pages. It boasts a comfortable GUI, an ability to create professional security audit and compliance reports, and tools for advanced manual webapp testing. Read 7 reviews. Latest release version 1. Nov. 1. 6, 2. 01. Qualys. Guard is a popular Saa. S software as a service vulnerability management offering.
11/3/2017
Posted by admin